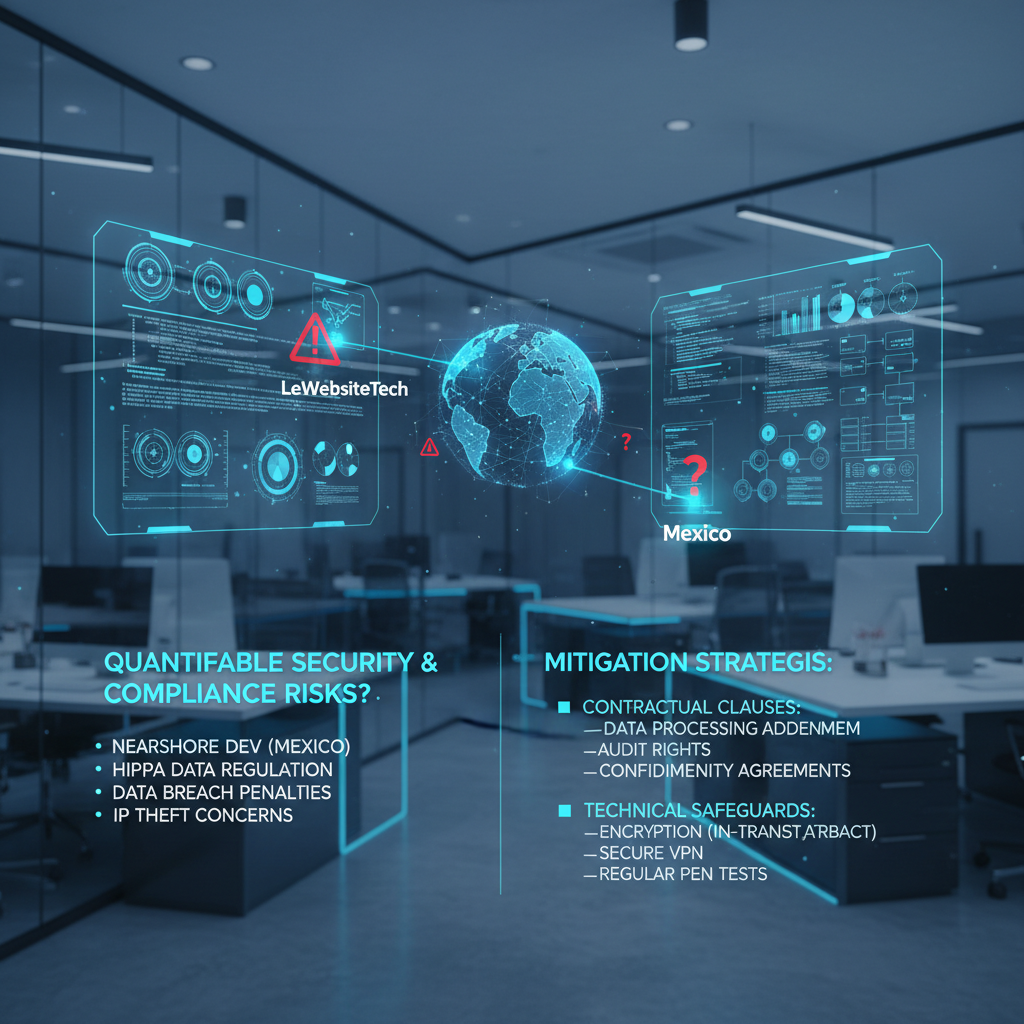
Quantifiable Security and Compliance Risks of Nearshore Development in Mexico (HIPAA) and Their Mitigation
Direct Answer Snippet: Navigating HIPAA Compliance in Mexican Nearshore Development
Nearshore development in Mexico presents quantifiable security risks related to HIPAA compliance, including data breaches, unauthorized access, and regulatory penalties. Mitigation involves robust contractual clauses specifying data handling protocols, incorporating technologies like end-to-end encryption within Python-based applications hosted on AWS, and implementing stringent access controls within React-powered frontends. A proactive, layered approach is critical to protecting sensitive patient data.
The Allure and the Peril: Nearshore Development and Data Security
The cost benefits of nearshore development in Mexico are undeniable. For US-based technology companies like LeWebsiteTech, leveraging Mexican talent for projects involving technologies like Python, React, and AWS infrastructure can significantly reduce operational expenses. However, when dealing with Protected Health Information (PHI) subject to HIPAA regulations, these benefits must be carefully weighed against the potential security and compliance risks.
Quantifying the Risks: What’s at Stake?
Failure to comply with HIPAA can result in significant financial penalties. The Office for Civil Rights (OCR) can impose fines ranging from $119 to $59,450 per violation, with annual caps reaching millions of dollars. Beyond the financial implications, data breaches erode customer trust, damage brand reputation, and can lead to costly litigation. Specifically, in a nearshore setting, these risks are amplified by factors such as:
- Data Residency: Ensuring PHI remains within compliant jurisdictions and adheres to data localization requirements, even when being processed in Mexico.
- Access Control: Implementing robust role-based access control (RBAC) to limit access to PHI only to authorized personnel, both in the US and in Mexico.
- Infrastructure Security: Securing the physical and digital infrastructure used to store and process PHI, including servers, networks, and cloud environments like AWS.
- Employee Training: Providing comprehensive HIPAA training to all personnel involved in handling PHI, regardless of their location.
- Vendor Management: Ensuring that any third-party vendors involved in the development process are also HIPAA compliant.
Contractual Safeguards: The Legal Foundation for Security
A well-crafted contract is the cornerstone of a secure and compliant nearshore development relationship. Key clauses to include are:
- Business Associate Agreement (BAA): A mandatory agreement that outlines the specific responsibilities of the Mexican development team (acting as a Business Associate) in protecting PHI.
- Data Security and Privacy Provisions: Clearly defining the permitted uses and disclosures of PHI, as well as the security measures that must be implemented.
- Incident Response Plan: Requiring the Mexican development team to have a comprehensive incident response plan in place to address any data breaches or security incidents.
- Audit Rights: Granting LeWebsiteTech the right to audit the Mexican development team’s security practices and procedures to ensure compliance.
- Indemnification Clause: Protecting LeWebsiteTech from any financial losses or liabilities resulting from the Mexican development team’s failure to comply with HIPAA.
Technical Safeguards: Hardening the Digital Perimeter
Contractual clauses alone are not enough. Implementing robust technical safeguards is essential to protect PHI from unauthorized access, use, or disclosure. These safeguards should include:
- Encryption: Implementing end-to-end encryption for all PHI, both in transit and at rest. This can be achieved using technologies like TLS/SSL for data in transit and AES encryption for data at rest within your AWS environment, all potentially managed through Python scripts for automated security.
- Access Controls: Enforcing strict access controls using RBAC to limit access to PHI only to authorized personnel. Multi-factor authentication (MFA) should be implemented for all users. React-based user interfaces can be designed with granular access control features.
- Security Audits and Vulnerability Scanning: Regularly conducting security audits and vulnerability scans to identify and address any weaknesses in the system.
- Intrusion Detection and Prevention Systems (IDPS): Deploying IDPS to detect and prevent malicious activity.
- Data Loss Prevention (DLP): Implementing DLP solutions to prevent sensitive data from leaving the organization’s control.
- Secure Coding Practices: Adhering to secure coding practices during the development process to prevent vulnerabilities that could be exploited by attackers. Training the development team in Mexico on secure coding practices for Python, React, and AWS is crucial.
Conclusion: Strategic Nearshoring with Confidence
Nearshore development in Mexico offers significant advantages, but it’s crucial to approach it with a comprehensive understanding of the associated security and compliance risks, particularly regarding HIPAA. By implementing robust contractual safeguards and technical measures, and focusing on proactive training and due diligence, LeWebsiteTech can leverage the benefits of nearshore development while ensuring the confidentiality, integrity, and availability of sensitive patient data. Prioritizing security and compliance isn’t just about avoiding penalties; it’s about building trust and maintaining a competitive edge in the healthcare technology landscape.
Subscribe to our
newsletter.
Get valuable strategy, culture, and brand insights straight to your inbox.
By signing up to receive emails from Motto, you agree to our Privacy Policy. We treat your info responsibly. Unsubscribe anytime.